This repository contains code for the following research.
"Total Recall: Persistence of Passwords in Android," Jaeho Lee, Ang Chen and Dan S. Wallach, The 26th Network and Distributed System Security Symposium (NDSS '19), San Diego, CA, USA, February 2019 [PDF] [Slides] [Slides_pptx] [BibTex]
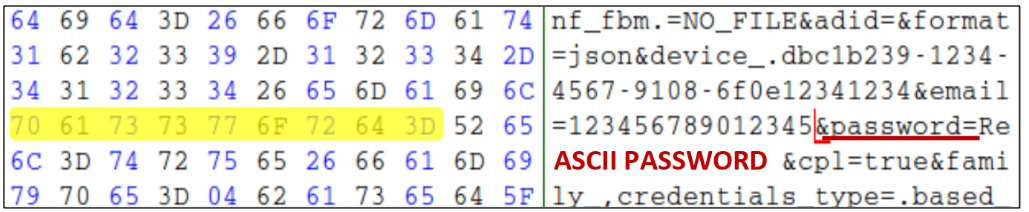
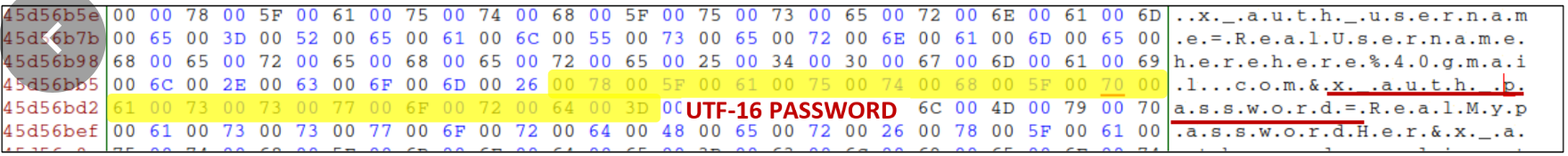
In memory disclosure attacks, an unprivileged attacker can steal sensitive data from device memory. A good security practice for handling sensitive data, such as passwords, is to overwrite the data buffers with zeros once the data is no longer in use. This protects against attackers who gain a snapshot of a device’s physical memory. For instance, the recent memory dumping vulnerability in the Nexus 5X phone allows an attacker to obtain the full memory dump of the device even if the phone is locked.
e.g., Google Nexus 5X Bootloader Unauthorized Memory Dumping via USB
However, the password retention in memory is widespread in Android, and password strings are easily recognizable from memory dump. The lack of support in the Android framework and developers' various mistakes cause this retention problem.
We offer two solutions:
- SecureTextView: a secure version of Android TextView that can eliminate password retention in the Android framework.
- KeyExporter: a simple abstraction for accessing passwords that helps developers follows stronger cryptographic practices to prevent password misuse.
- apps: list of analyzed password authentication apps
- pmdump: process memory acquisition tool on Linux or Android
- keyexporter: Standalone KeyExporter APIs
- SecureTextView: Android framework patch for SecureTextView
- lockscreen_patch: Android framework patch for lockscreen process
- evaluation: apps after applying KeyExporter APIs